Quicklizard may provide you with updates regarding our products, tips, etc. You may unsubscribe from these communications at any time.



At Quicklizard, safeguarding your data is our top priority. That’s why we’re proud to be SOC 1 Type 2 certified, demonstrating our commitment to operational excellence and data integrity. This rigorous certification involves an independent audit of our internal controls over financial reporting, ensuring that our systems and processes meet the highest standards of security, availability, and accuracy. It’s our assurance to you that your data is handled with reliability and transparency every step of the way.

At Quicklizard, data privacy is a top priority. We are fully committed to complying with the General Data Protection Regulation (GDPR), ensuring that our platform and processes meet the highest standards of data protection. Our services do not require personally identifiable information (PII) to operate, minimizing data privacy risks from the start. We implement strong encryption, rigorous access controls, and maintain a robust privacy management framework aligned with industry best practices. Additionally, our multi-tenancy architecture ensures complete data separation between customers, and we do not use customer data for AI training. With a dedicated focus on transparency, security, and compliance, we provide our customers with the confidence that their data is handled responsibly and securely.

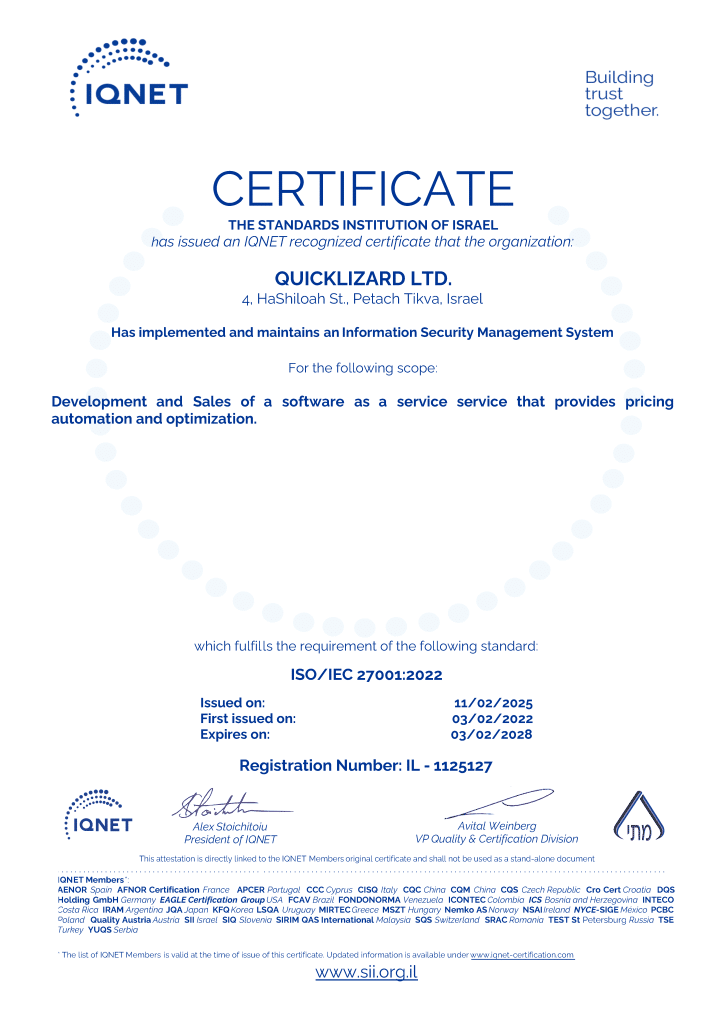
At Quicklizard, protecting your data is paramount. That’s why we’re proud to be ISO 27001 certified, the world’s leading standard for information security management. This rigorous certification means we have a robust system in place to safeguard your information, from regular risk assessments to comprehensive security controls. It’s our promise to handle your data with the utmost confidentiality and integrity.


Quicklizard prioritizes the safeguarding of user information, employing encryption measures for data both at rest and in transit across all servers. Our systems are designed to ensure data is protected at all times. Specifically, TLS v1.2 is implemented with formidable ciphers to fortify data security during transit.


At Rest
All at-rest sensitive user data is encrypted. We use the industry standard encryption at the storage level.
As part of our commitment to maintaining an information security framework, we conduct an annual Information Security Awareness Training for all our employees. This comprehensive program ensures that our team remains vigilant and well-informed about the latest cybersecurity threats and best practices. Covering topics such as data protection, phishing awareness, and secure online practices, this training empowers our employees to be proactive guardians of sensitive information. By fostering a culture of heightened awareness, we strengthen our collective defense against potential risks, safeguarding both our internal operations and the valuable data entrusted to us by our clients and partners.

We commit to annual third party penetration tests, simulating real-world cyberattacks to expose and patch any vulnerabilities before bad actors can exploit them. The vulnerabilities remediation is performed according to a strict timeline as required in our internal policies. This dedication to proactive security ensures your information is constantly protected.

Our dedication revolves around ensuring best practices for the protection and use of customer data. The Quicklizard architecture is designed with a focus on redundancy, security, and availability. In terms of security, our design adheres to industry best practices, which now includes alignment with the OWASP Top 10 to address the most critical web application security risks. This comprehensive approach encompasses encrypted transmissions, prevention of cross-site scripting, firewalls, routine security updates, thorough security scans, and vulnerability assessments. By integrating OWASP Top 10 guidelines, we further fortify our defenses against injection flaws, broken authentication, sensitive data exposure, and other prevalent security vulnerabilities. These practices collectively ensure the utmost security for your data, demonstrating our commitment to maintaining a robust security posture.
Tariffs Are Paused. Use This Window to Build a Smarter Pricing Response. Learn How